Maintaining credentials is crucial for building trust and ensuring the security of customer  technology environments and personal information. Annually, Apps Associates engages a licensed and accredited independent third party to perform SOC 1 Type 2 and SOC 2 Type 2 testing. For additional details about SOC reporting and its standards, please visit the website of the American Institute of Certified Public Accountants (AICPA).
technology environments and personal information. Annually, Apps Associates engages a licensed and accredited independent third party to perform SOC 1 Type 2 and SOC 2 Type 2 testing. For additional details about SOC reporting and its standards, please visit the website of the American Institute of Certified Public Accountants (AICPA).
Credentials Assurance
Customer Security Validation and Audit Self Service
At Apps Associates, security is a top priority, which is why we’ve adopted a security-by-design approach throughout our services and business processes. Our goal is to ensure our customers feel confident that their information is always handled securely. To help streamline your vendor assessment process, we offer an on-demand self-service site with an overview of Apps Associates’ security, privacy, and compliance practices. This site includes detailed responses to the Standardized Information Gathering (SIG) core questionnaire, AICPA certifications, and access to relevant policies and reports.

Utilizing best-of-breed technologies and implementing stringent protocols, methodologies, and policies clients can have confidence that their services are well-protected. With a dedicated team of experts, continuous monitoring, and a proactive approach to identifying and mitigating vulnerabilities, we aim to provide the highest level of security in the delivery of our managed services. This commitment instills confidence in our clients and establishes Apps Associates as a trusted partner in the realm of secure and reliable solutions. Therefore, we encourage our customers to leverage existing Apps Associate’s security-focused solutions and services, providing the most holistic and integrated approach in the protection of customer assets.
Apps Associates also collaborates closely with our customers to ensure they remain informed of important security updates essential to the protection of their data and systems. Timely communication and technical expertise help prevent potential security breaches or interruptions to critical customer services.
Apps Associates’ Security in Managed Customer Services
Security is of the utmost importance to us, and we understand security is an ongoing journey. At Apps Associates, we prioritize security by incorporating a multi layered approach into our services, infrastructure, and business processes which are continuously monitored by the security and compliance teams and kept current. This approach reflects a proactive and comprehensive strategy to ensure the safety and trustworthiness of the services we provide.
The program is built upon a control framework designed to protect against anticipated threats to the security and integrity of Apps Associates and customer information. We embrace:
- Alignment with Industry Standards:
Salesforce, Oracle, JD Edwards, PeopleSoft, Siebel, Hyperion, OBIEE, Fusion Middleware, Microsoft, Boomi - Multi-Layered Security Approach:
Employing a multi-layered security approach involves implementing various security measures at various levels of the organization, infrastructure, and business processes. This strategy strengthens the cybersecurity posture by providing multiple lines of defense against potential threats. - Data Security and Privacy: Our focus on managing customer information safely is paramount. This commitment to data security helps to build trust with our customers who rely on Apps Associates to protect their sensitive information in performance of the services.
- Continuous Adaption: We recognize that the threat landscape is constantly evolving, and it is important to continuously update and adapt current security measures to support preparedness with emerging security challenges.
- Continuous Monitoring: Real-time monitoring of security measures and infrastructure is essential in the identification and timely response to security vulnerabilities and incidents.
- Customer Compliance Management: Effective customer compliance management is essential in fostering trust with our customers. Identification of unique customer compliance requirements are recorded and tracked in the Enterprise Governance, Risk, and Compliance module. Requirements are distributed to applicable service and support teams to ensure awareness and conformity. Formal acknowledgements are collected and retained for audit purposes.
Ensuring the sanctity of customer security is the bedrock upon which trust and reliability in any enterprise are built. At the heart of our commitment lies a robust framework defined by seven pillars of Customer Security Management. These pillars serve as the foundational principles guiding our determined pursuit of safeguarding sensitive information, upholding privacy, and fostering a secure environment for our valued partners. Each pillar represents a cornerstone in our holistic approach, fortifying our dedication to proactive, comprehensive, and cutting-edge strategies aimed at fortifying the integrity of our customers’ data and fostering a resilient security ecosystem.
The Apps Associates’ Core Security Program
Customer Security Management
Operational Risk Management
Apps Associates’ robust risk management framework is designed to safeguard against hazards and disruptions resulting in steadfast customer service delivery. It includes risk identification, risk assessment, risk mitigation, continuous monitoring, and regular reporting to members of the Apps leadership team.
Business Resilience
Ensuring unwavering business resilience is of utmost importance in today’s dynamic threat landscape. The Apps Associates’ Business Continuity and Disaster Recovery Program is reviewed and updated regularly to include threat evaluation, business continuity plans, and notification procedures. Advanced encryption, real-time threat monitoring, proactive risk mitigation, and regular patch management are consistently prioritized to mitigate risks and ensure continuity.
Security Testing & Analysis
Our dedication to supplying secure services is reinforced by our proactive strategy, which places a high priority on the confidentiality, integrity, and availability of customer information. A certified, independent 3rd party performs quarterly internal and external vulnerability and penetration testing. Findings are prioritized and remediated in a timely manner.
Third Party Risk Management (TPRM)
Apps Associates’ third-party assessment program is designed to ensure the security, compliance, and overall reliability of our vendors and partners. A standardized framework is used that covers key areas such as security, compliance, financial stability, and performance. Third parties are prioritized based on risk level and continuous monitoring is employed.
Incident Response
Incident response is a critical part of Apps Associates cybersecurity strategy. This program has been designed to effectively manage security incidents to minimize damage and reduce recovery times. The incident response plan includes classification, prioritization, dedicated teams, communication plan, containment, eradication, and forensic analysis. Tabletop exercises are performed twice a year to further confirm preparedness and the program is updated annually.
Enterprise Awareness Training
Security measures are only as strong as the people implementing them. Providing employees with training on relevant laws, regulations, and company policies helps to ensure they are aware of and adhere to compliance requirements. Apps Associates has implemented a continuous “micro” learning program that provides consistent training throughout the year to ensure safeguarding data is kept front of mind.
Phishing simulations are performed quarterly, and results are appraised by the Apps Associates’ leadership team. Personalized training is offered to employees to further facilitate awareness and understanding.
Monthly security newsletters are distributed that include information on relevant security practices and new vulnerabilities that may have an impact on business services.
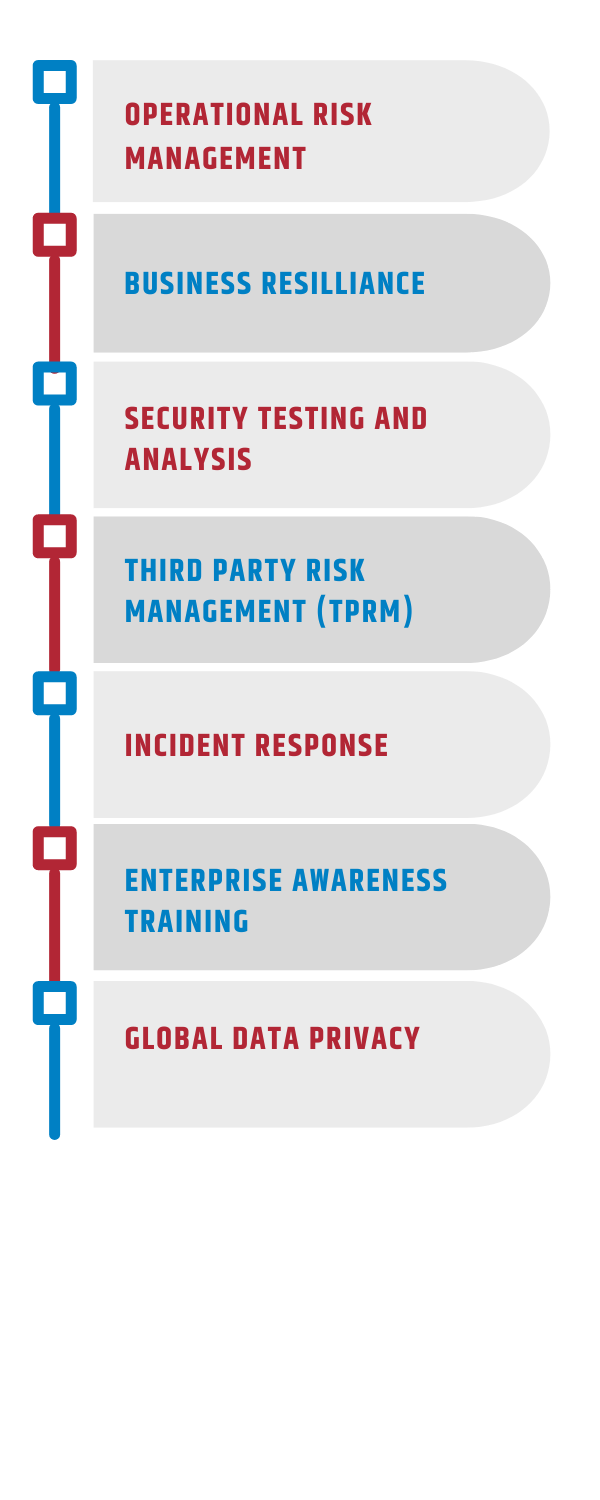
Global Data Privacy
The Apps Associates’ Corporate Governance Team oversees principles, regulations, and practices governing the protection of personal data that have been adopted worldwide.
The enterprise governance, risk, and compliance (GRC) platform is used to track all privacy-related activities and proactive compliance efforts in the protection of individual personal data as a fundamental aspect of business operations.
Apps Associates’ global clientele rely on the company to manage their confidential data by taking the following measures:
- Safeguarding and overseeing the handling of personal data: This involves implementing security measures and protocols to ensure the confidentiality, integrity, and availability of personal data. It may include encryption, access controls, and secure storage practices.
- Performing privacy assessments: Regular privacy assessments help identify potential risks and vulnerabilities in the handling of personal data. These assessments involve reviewing processes, policies, and technical infrastructure to ensure they align with privacy requirements.
- Guaranteeing suitable privacy safeguards: Apps Associates is committed to implementing appropriate measures to protect personal data. These safeguards include technological solutions, employee training, and ongoing monitoring to ensure compliance.
- Assessing privacy breaches: In the event of a privacy breach, Apps Associates conducts assessments to understand the scope of the breach, identify affected individuals, and take appropriate remedial actions. This is crucial for compliance with data privacy regulations and to mitigate potential harm.
- Establishing comprehensive enterprise-level initiatives: A proactive approach to compliance is employed by implementing broader initiatives that cover all aspects of the enterprise. This includes developing and updating policies, procedures, and training programs to address changes in regulations and legislation.
- Staying in compliance with changes to regulations and new legislation: Apps Associates is dedicated to staying abreast of changes in data privacy regulations and adapting its practices accordingly. This involves continuous monitoring of legal developments and making necessary adjustments to ensure ongoing compliance.
In summary, these measures collectively demonstrate a commitment to maintaining an elevated level of data privacy and security for Apps Associates’ global clientele. It aligns with best practices for organizations that oversee sensitive and confidential information, especially in the context of evolving data privacy regulations. The policy is reviewed on an annual basis and modified as required.